In today’s digitally interconnected world, safeguarding our online presence has become more crucial than ever. Whether you want to protect your sensitive data from prying eyes or access geo-restricted content, a reliable VPN can be your go-to solution. As highly skilled SEO specialists and expert copywriters, we bring you a comprehensive guide to the top-notch VPN options for iPhone users, equipping you with the knowledge to make informed decisions and ensuring your online activities remain secure and private.
Understanding the Benefits of VPNs for iPhone
Before delving into the specifics of the best iOS VPNs, let’s take a moment to understand the invaluable benefits they offer to iPhone users:
1. Enhanced Privacy and Security
By funneling your internet traffic through encrypted tunnels, VPNs shield your data from potential hackers and cybercriminals. Your online activities remain anonymous, giving you the confidence to browse the web securely, even on public Wi-Fi networks.
2. Accessing Geo-Restricted Content
VPN services can virtually relocate your iPhone’s IP address to a different country, granting you access to geo-blocked content and streaming platforms that might not be available in your region.
3. Bypassing Censorship
In regions where internet censorship is prevalent, a dependable VPN can be your ticket to a free and unrestricted internet, allowing you to bypass content restrictions imposed by governments or internet service providers.
4. Streaming Accessibility
Free iPhone VPNs can be incredibly useful for accessing geo-restricted streaming content. By connecting to a server in another country, users can bypass content restrictions and enjoy their favorite shows and movies on platforms like Netflix, Hulu, or Disney+.
5. Securing Public Wi-Fi
When connecting to public Wi-Fi networks, such as those found in coffee shops, airports, or hotels, your data becomes vulnerable to hackers and cybercriminals. Free VPNs encrypt your traffic, adding an extra layer of security and protecting your sensitive information from potential threats.
6. Occasional Sensitive Searches
If you need to perform occasional sensitive searches and wish to maintain your privacy, a free iPhone VPN can be a suitable option. By masking your IP address and encrypting your data, you can browse the web with confidence, knowing that your online activities remain confidential.
Limitations of Free iPhone VPNs
1. Data Limits
Most free VPN providers impose data caps on their users. While this might be sufficient for light browsing or occasional streaming, it can quickly become insufficient for more data-intensive activities.
2. Limited Server Options
Free VPNs usually offer a limited number of servers compared to their paid counterparts. This can result in slower connection speeds and may not be ideal for users seeking a wide range of server locations.
3. Lack of P2P Support
Peer-to-peer (P2P) file sharing is often restricted or completely disallowed on free VPN plans. If you engage in torrenting or other P2P activities, a free VPN may not be the best fit.
Choosing the Right VPN: Factors to Consider
Selecting the ideal VPN for your needs requires careful consideration of various factors. To make an informed choice, here are essential aspects to evaluate when exploring VPN options:
1. Privacy and Security:
Look for a VPN that employs robust encryption protocols, a strict no-logs policy, and advanced security features to keep your data safe and private.
2. Server Locations:
The more server locations a VPN offers, the more flexibility you have in accessing geo-restricted content from different regions.
3. Internet Speed Impact:
As mentioned earlier, modern VPNs aim to minimize speed drops, but it’s still essential to ensure that your chosen VPN doesn’t significantly impact your browsing speed.
4. Ease of Use:
A user-friendly interface and intuitive setup process can enhance your overall VPN experience.
5. Customer Support:
Look for a VPN provider with reliable customer support to assist you in case of any issues or queries.
6. Pricing:
While cost is a consideration, prioritize the value and features a VPN offers rather than solely focusing on the price.
The Top iOS VPNs: Striking the Perfect Balance
Now, let’s explore the crème de la crème of iOS VPNs, where both paid and trustworthy free options coexist, each offering distinct advantages for iPhone users.
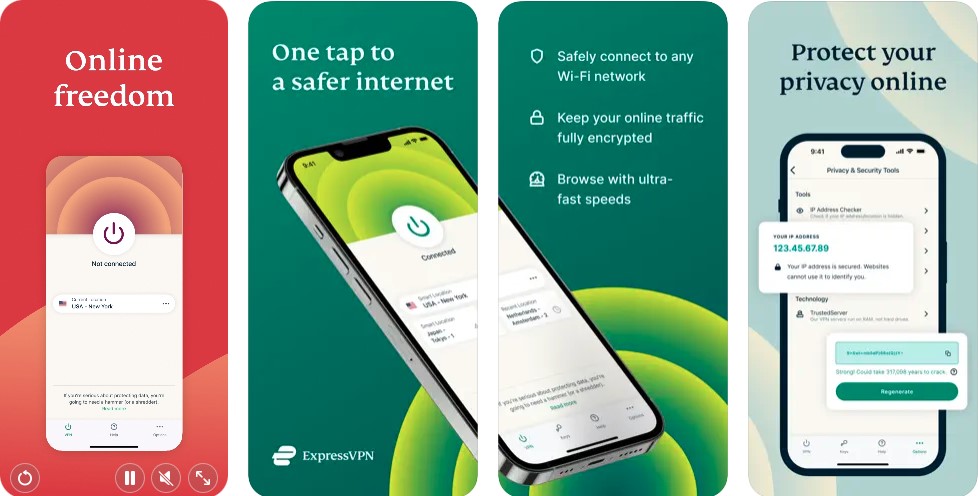
1. ExpressVPN – The Premium Choice
When it comes to top-tier VPN services, ExpressVPN stands out as a formidable option. With its user-friendly interface and lightning-fast speeds, this paid VPN service offers a risk-free trial, enabling you to experience its remarkable features before committing fully.
2. Hotspot Shield – The Trustworthy Free VPN
For users seeking a reliable free VPN, Hotspot Shield emerges as a strong contender. While it may have limitations on data and speed, it excels in terms of privacy and security, making it an excellent choice for safeguarding your online presence.
3. Hide.me – The Reliable Free VPN
Hide.me proves to be a dependable free VPN option, offering 10GB of monthly usage and fast speeds. With a focus on privacy and encryption, it ensures your data remains protected during your internet escapades.
4. ProtonVPN – Privacy and Censorship Freedom
If bypassing censorship and ensuring privacy are your primary concerns, ProtonVPN has got you covered. Though accessing Netflix US may require payment, its capabilities in navigating restricted content make it worth considering.
Proton VPN is another reliable free VPN choice for iPhone users. It boasts unlimited data, allowing you to browse without worrying about data caps. Proton VPN also uses the WireGuard protocol with XChaCha20 encryption to ensure your data remains private and secure.
While the free version is sufficient for basic security needs, it lacks some of the advanced features available in the premium version, which starts at $4.99/month. However, for users seeking a free and privacy-focused VPN, Proton VPN remains an excellent option.
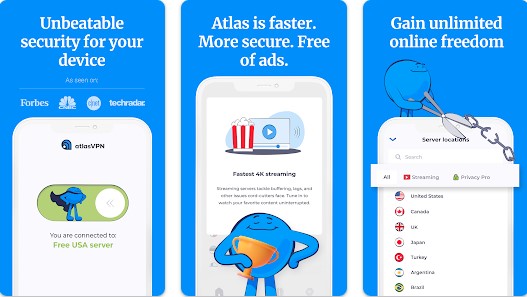
5. AtlasVPN – A Balance of Features
Despite lacking OpenVPN encryption, AtlasVPN impresses with its good speeds, no-logs policy, and a kill-switch feature, promising a secure and private browsing experience.
Atlas VPN stands out among free VPN providers due to its commitment to security and privacy. It employs the WireGuard protocol with XChaCha20 encryption, ensuring your data remains well-protected. The service also comes with a kill switch feature, which adds an extra layer of security by cutting off internet access if the VPN connection drops unexpectedly.
With Atlas VPN’s free version, users get a generous 5GB data limit and, on average, retain 90% of their initial download speed, making it a viable option for moderate usage. However, it’s worth noting that the free version does not bypass geo-restrictions, limiting access to certain content. For an enhanced experience, users can opt for the paid version, starting at a budget-friendly $1.82/month, which unlocks more features, unlimited data, and servers in various countries.
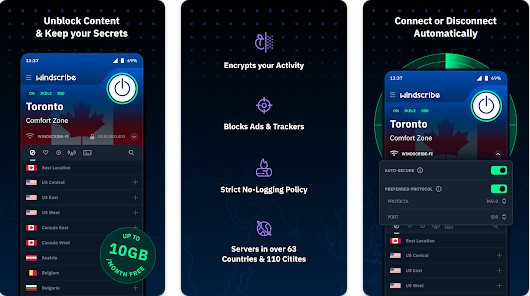
6. Windscribe – Strong Privacy and Generous Data
Lastly, Windscribe offers strong privacy and encryption protocols, granting 10GB of data per month to free users. While it might have slightly slower free servers, its overall performance makes it an attractive option.
Windscribe is known for its user-friendly interface and transparent approach to privacy. It provides a generous 10GB of monthly data for free users, making it suitable for occasional browsing and light tasks. Windscribe utilizes strong encryption protocols to protect your data while in transit.
While the free version might not be ideal for heavy streaming or data-intensive activities, it still offers adequate security for everyday internet use. Users looking for a broader range of features and unlimited data can consider upgrading to Windscribe’s paid plans.
Making the Right Choice for Your iPhone
Choosing the perfect VPN for your iPhone depends on your specific needs and preferences. Paid VPNs like ExpressVPN guarantee premium features and unparalleled support, while free VPNs like Hotspot Shield, Hide.me, ProtonVPN, AtlasVPN, and Windscribe provide viable alternatives for those looking to prioritize privacy and security without breaking the bank.
In conclusion, safeguarding your digital life with a reputable VPN should be a top priority for all iPhone users. With our carefully curated list of the best iOS VPNs, you can now navigate the digital landscape with confidence, unlocking a world of privacy, security, and unrestricted content access at your fingertips.